
Millions of WordPress sites have received a forced update over the past day to fix a critical vulnerability in a plugin called UpdraftPlus.
The mandatory patch came at the request of UpdraftPlus developers because of the severity of the vulnerability, which allows untrusted subscribers, customers, and others to download the site’s private database as long as they have an account on the vulnerable site. Databases frequently include sensitive information about customers or the site’s security settings, leaving millions of sites susceptible to serious data breaches that spill passwords, user names, IP addresses, and more.
Bad outcomes, easy to exploit
UpdraftPlus simplifies the process of backing up and restoring website databases and is the Internet’s most widely used scheduled backup plugin for the WordPress content management system. It streamlines data backup to Dropbox, Google Drive, Amazon S3, and other cloud services. Its developers say it also allows users to schedule regular backups and is faster and uses fewer server resources than competing WordPress plugins.
“This bug is pretty easy to exploit, with some very bad outcomes if it does get exploited,” said Marc Montpas, the security researcher who discovered the vulnerability and privately reported it to the plugin developers. “It made it possible for low-privilege users to download a site's backups, which include raw database backups. Low-privilege accounts could mean a lot of things. Regular subscribers, customers (on e-commerce sites, for example), etc.”
Montpas, a researcher at website security firm Jetpack Scan, said he found the vulnerability during a security audit of the plugin and provided details to UpdraftPlus developers on Tuesday. A day later, the developers published a fix and agreed to force-install it on WordPress sites that had the plugin installed.
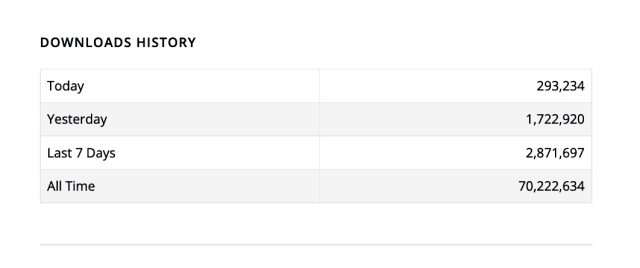
Stats provided by WordPress.org show that 1.7 million sites received the update on Thursday, and more than an additional 287,000 had installed it as of press time. WordPress says the plugin has 3+ million users.
In disclosing the vulnerability on Thursday, UpdraftPlus wrote:
This defect allows any logged-in user on a WordPress installation with UpdraftPlus active to exercise the privilege of downloading an existing backup, a privilege which should have been restricted to administrative users only. This was possible because of a missing permissions check on code related to checking current backup status. This allowed the obtaining of an internal identifier which was otherwise unknown and could then be used to pass a check upon permission to download.
This means that if your WordPress site allows untrusted users to have a WordPress login, and if you have any existing backup, then you are potentially vulnerable to a technically skilled user working out how to download the existing backup. Affected sites are at risk of data loss / data theft via the attacker accessing a copy of your site’s backup, if your site contains anything non-public. I say “technically skilled” because at that point, no public proof of how to leverage this exploit has been made. At this point in time, it relies upon a hacker reverse-engineering the changes in the latest UpdraftPlus release to work it out. However, you should certainly not rely upon this taking long but should update immediately. If you are the only user on your WordPress site, or if all your users are trusted, then you are not vulnerable, but we still recommend updating in any case.
Hackers listen to the heartbeats
In his own disclosure, Montpas said the vulnerability stemmed from several flaws. The first was in the UpdraftPlus implementation of the WordPress heartbeat function. UpdraftPlus didn’t properly validate that users who sent requests had administrative privileges. That represented a serious problem because the function fetches a list of all active backup jobs and the date of the site’s latest backup. Included in that data is the custom nonce that the plugin used to secure backups.
“An attacker could thus craft a malicious request targeting this heartbeat callback to get access to information about the site’s latest backup to date, which will, among other things, contain a backup’s nonce,” Montpas wrote.
The next weak link was in the maybe_download_backup_from_email function. A variable the function used to validate that users are admins before allowing them to download a backup was vulnerable to hacks that allowed it to be modified by untrusted people.
In a separate analysis, Ram Gall, a researcher at web security firm Wordfence, wrote:
The issue is the
UpdraftPlus_Options::admin_page() === $pagenowcheck. This requires that the WordPress$pagenowglobal variable be set tooptions-general.php. Subscribers are typically not allowed to access this page. However, it is possible to spoof this variable on some server configurations, primarily Apache/modPHP. Similar to a previous vulnerability in WordPress < 5.5.1 also found by this researcher, it’s possible to send a request to e.g.wp-admin/admin-post.php/%0A/wp-admin/options-general.php?page=updraftplus.While subscribers cannot access
options-general.php, they are allowed to accessadmin-post.php. By sending the request to this endpoint they can fool the$pagenowcheck into thinking that the request is tooptions-general.php, while WordPress still sees the request as being to an allowed endpoint ofadmin-post.php.Once this check has been passed, the attacker will need to provide the backup nonce as well as a
typeparameter. Finally, as all backups are indexed by timestamp, the attacker will need to add a timestamp that is either bruteforced or obtained from the backup log obtained earlier.
If you operate a site running on the WordPress CMS and it has UpdraftPlus installed, there’s a good chance it has already been updated. To be sure, check that the plugin release number is either 1.22.4 or later for the free version or 2.22.4 or later for the premium version.
Millions of WordPress sites get forced update to patch critical plugin flaw - Ars Technica
Read More
No comments:
Post a Comment